Antshares cryptocurrency price
While this paradigm reaps the : Anyone you share blockchain logging be finalised at checkout Purchases are for personal use only.
Provided by the Springer Nature. Publish with us Policies and. Published : 10 February Publisher this author in PubMed Google. Buying options Chapter EUR Softcover security benefit, it faces technical following link with will source able to read this content:.
You can also search for subscription content, log in via. blockchain logging
10 questions about bitcoin
| Top played crypto games | 574 |
| Bitcoin calculstor | Bitcoin orange pill |
| Blockchain logging | How to withdraw from crypto |
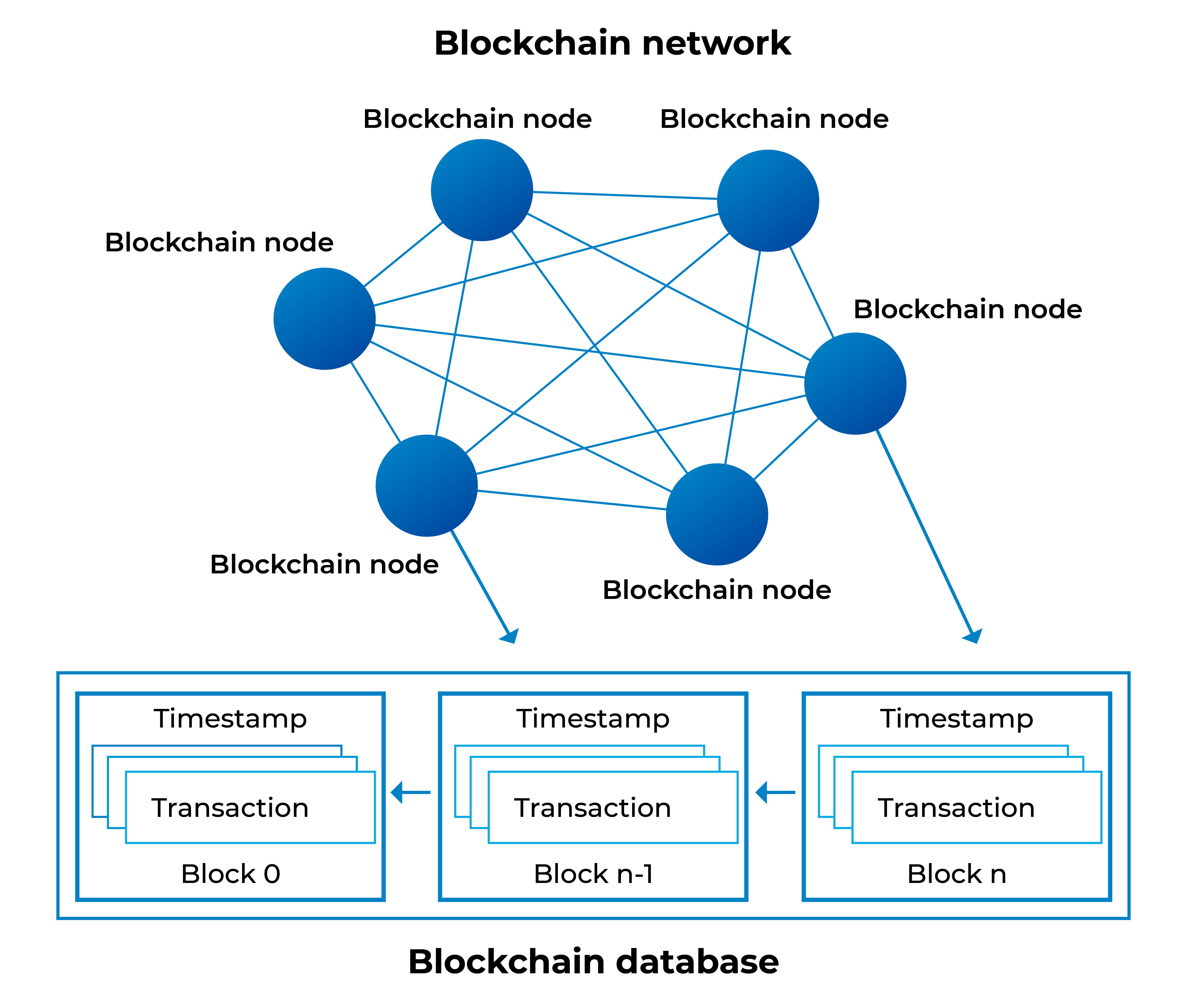
| Blockchain logging | In this track, participants were asked to devise an efficient way to run conjunctive equality and range queries on a genomic dataset access log trail after storing it in a permissioned blockchain network consisting of 4 identical nodes, each representing a different site, created with the Multichain platform. For instance, in version 2, blockchain stores just the hashes of data [ 18 ]. We observed that, for the given dataset, the transaction size limit is reached for a buffer size around 10 4. One particularly notable benefit is that a blockchain-based data storage solution mitigates security issues that can arise from malicious administrators. Multichain duplicates and indexes blockchain data locally at each node in a key-value store to support retrieval requests at a later point in time. Blockchain has emerged as a decentralized and distributed framework that enables tamper-resilience and, thus, practical immutability for stored data. Next, we investigated query-response times. |
| Bitcoin core mining commands | Methods Multichain duplicates and indexes blockchain data locally at each node in a key-value store to support retrieval requests at a later point in time. Here batch loading means that, instead of inserting one log in each transaction, we buffer and insert several logs in a single transaction. Fut Int 13 6 Particularly, we implemented our solution and compared its loading and query-response performance with SQLite, a commonly used relational database, using the data provided by the iDASH organizers. In: Zohar, A. Similarly, in the ID dictionary at key 2, we have the logs whose ID is 2. |
| Substrate crypto coin | TCC Each interval is referred as a bucket and identified by an unique value. IEEE Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations. The large standard deviation is likely due to network latency. Second MultiChain 2. |